Your AI Just Deployed Code. Who Signed It?
February 2026
Your AI agent just pushed to main.
It passed CI.
It deployed to production.
Who approved it?
Not a human. Not a policy. Nobody.
That's the gap.
The Problem Isn't AI Writing Code
AI writing code is fine. AI agents committing to repos is fine. Autonomous systems making changes faster than humans can review—that's the whole point.
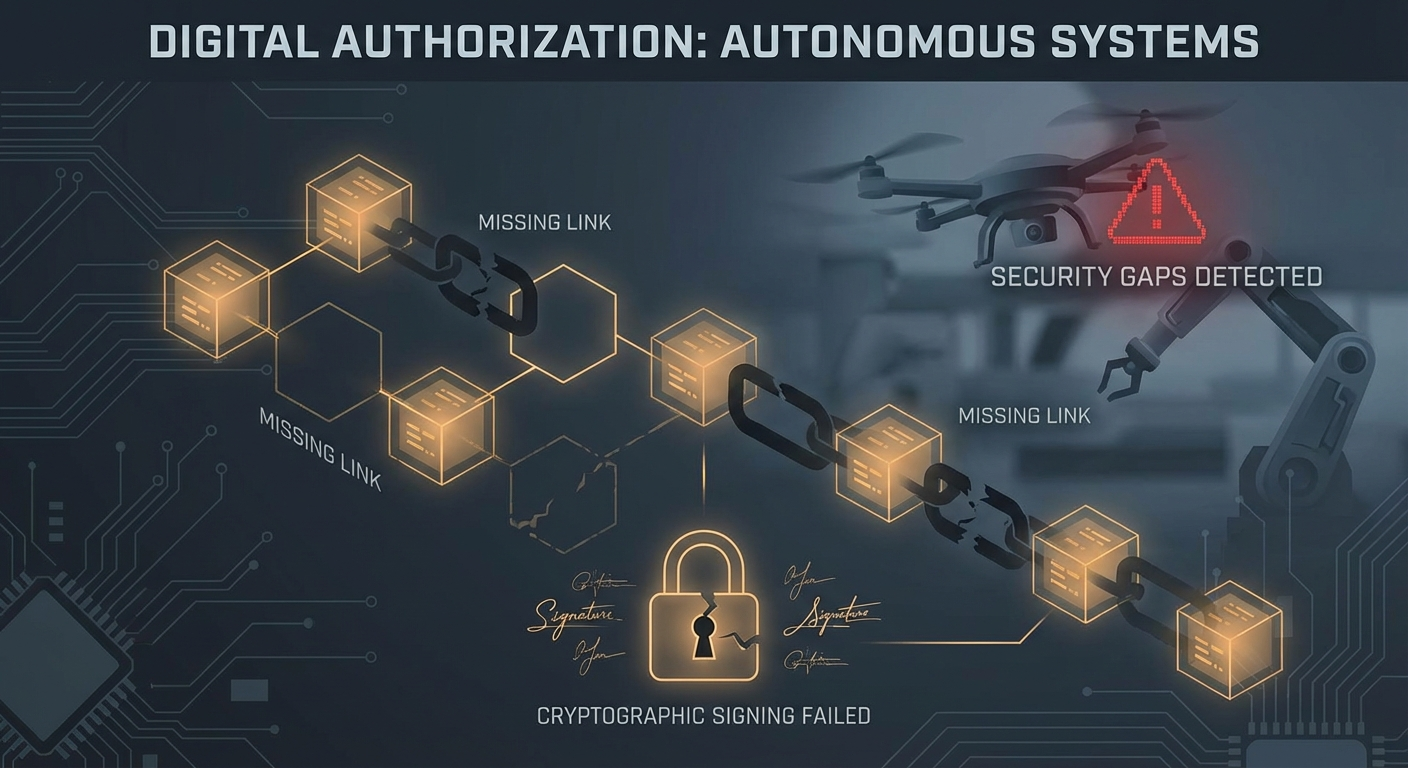
The problem is the authorization layer between "code exists" and "code runs in production."
Right now, that layer is:
- A merge button someone clicked
- A CI pipeline that passed
- An auto-deploy that triggered
None of these are authorization. They're automation.
The Signer of Record
Every production deployment needs a signer of record. Someone—or some policy—that explicitly says: yes, this specific change is authorized to run in production.
Not "the tests passed."
Not "someone merged it."
Not "it looks fine."
A cryptographic receipt. Immutable. Auditable. Signed.
What This Looks Like
{
"status": "APPROVED",
"scope": {
"repo": "acme/backend",
"sha": "abc123",
"env": "production"
},
"approver": "alice@acme.com",
"signature": "0x...",
"expiresAt": "2026-02-21T00:00:00Z"
}No receipt? No deploy. Period.
This isn't bureaucracy. It's accountability.
The Question You Should Ask
Go look at your last production deployment.
Can you answer:
- Who specifically authorized it?
- What exactly did they authorize?
- When did they authorize it?
- Is there a cryptographic proof?
If you can't answer all four, you have a gap.
And that gap grows wider every time you ship faster.
Add a deploy gate to your repo. Two minutes. Zero outages.
Install Deploy Gate →